Torzon Onion — Complete Market Overview
An in-depth informational analysis of Torzon Onion, covering platform architecture, security systems, vendor infrastructure, and operational characteristics of one of the darknet's most established marketplaces. All content is strictly educational.
Platform Architecture
Torzon Market operates as a Tor hidden service — a website accessible exclusively through the Tor anonymity network at an .onion address. Hidden services route all traffic through the Tor network bidirectionally, meaning neither the server hosting the market nor its users can be trivially identified by monitoring network traffic. The Torzon darknet platform uses v3 onion addresses (56-character base32 encoded addresses) which are cryptographically generated and tied to the service's private key.
The market's backend infrastructure is designed for resilience. Multiple redundant mirrors allow the service to remain accessible even when individual nodes face disruption. Server-side, the platform runs on hardened Linux distributions with extensive logging disabled and minimal attack surface. All communication between the user's browser and the hidden service is encrypted end-to-end through Tor's layered encryption — no man-in-the-middle position exists within the Tor circuit that can see both the traffic and the user's identity.
User accounts on Torzon Market require only a username and password — no email address, phone number, or other identifying information. Vendors go through a more intensive verification process including bond deposits and administrator review, which serves to deter exit scams and low-quality listings. The Torzon Market account system uses secure password hashing (bcrypt) and optional 2FA via TOTP authenticator applications or PGP-signed login confirmations.
12 Core Platform Features
A detailed breakdown of the primary systems that define Torzon Market's operational capabilities and security posture.
End-to-End Encryption
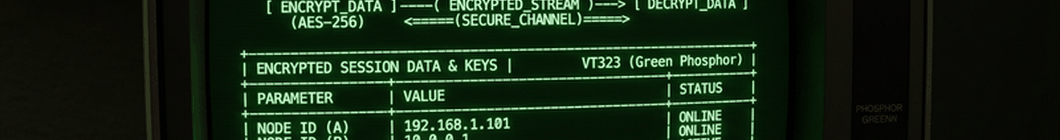
All data transmitted between users and the Torzon platform is encrypted through multiple layers: Tor's own layered encryption (three independent AES-256 layers) plus TLS at the application layer. Vendor-buyer messages additionally require PGP encryption, meaning even marketplace administrators cannot read communications.
Multi-Vendor Structure
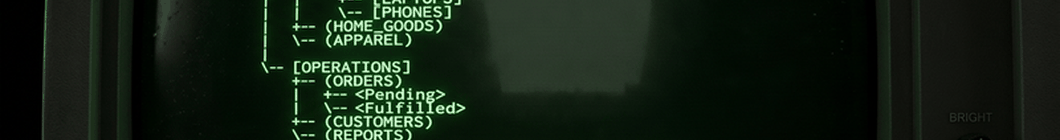
Torzon operates as a true multi-vendor marketplace with thousands of independent vendors offering products across dozens of categories. Vendors compete on price, reliability, and reputation, creating natural market incentives for quality. Category hierarchies are clearly organized and searchable with advanced filter options.
Multi-Signature Escrow
The escrow system uses 2-of-3 multi-signature cryptocurrency addresses. A transaction requires signatures from two of three parties (buyer, vendor, market) to release. This means funds cannot be stolen by a single actor — even a compromised market administrator cannot steal funds without also compromising the vendor or buyer's cryptographic key.
Tor Hidden Service Integration
Torzon's entire operation is built on the Tor hidden service protocol. The platform generates introduction points in the Tor network and maintains rendezvous circuits that allow users to connect without revealing either party's network location. The hidden service descriptor is cryptographically signed with the service's private key.
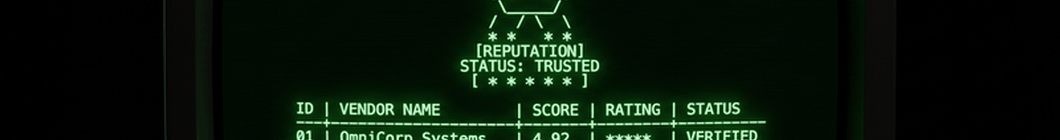
Vendor Reputation System
Each vendor builds a verifiable reputation through transaction history, buyer reviews, and trust scores. Reviews include delivery speed, stealth rating, product quality, and communication ratings. Vendors with sustained high scores earn Trusted Vendor status. The system is resistant to manipulation through bond requirements and review authentication.
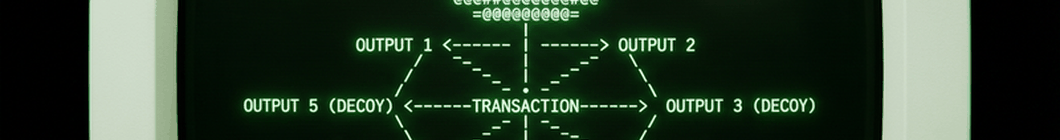
Monero-First Payments
Monero (XMR) is the primary payment method, providing transaction-level privacy through ring signatures, stealth addresses, and RingCT. Torzon's built-in Monero wallet handles address generation and transaction broadcasting. All XMR transactions are non-custodial where possible, and the platform's escrow uses dedicated multisig addresses per order.
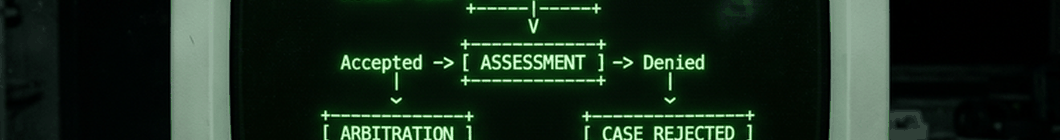
Dispute Resolution
An integrated arbitration system handles conflicts between buyers and vendors. Either party can open a dispute within the allowed window, providing evidence through the encrypted messaging system. Trained moderators review submitted evidence (tracking numbers, photographs, communication logs) and issue binding decisions. Resolution typically occurs within 24-72 hours.
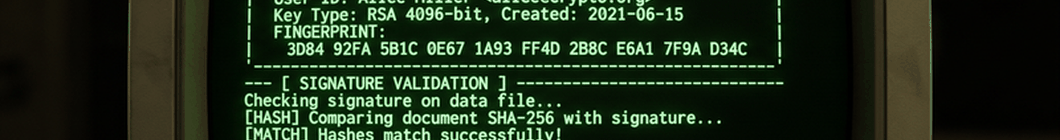
PGP Key Infrastructure
Every vendor account includes a published PGP public key, and buyers can verify vendor authenticity against these keys. The platform supports 4096-bit RSA and elliptic curve PGP keys. Vendor PGP keys are signed by the market's master key, creating a web of trust. All administrative announcements are PGP-signed for authenticity verification.
Advanced Search & Filters
The search system supports keyword search, category filtering, price range selection, vendor rating thresholds, and shipping origin/destination filters. Users can sort by price, rating, number of reviews, or recency. Saved searches and watchlists allow users to monitor specific vendors or product categories. The search index is updated in real-time as listings are modified.
Stealth Delivery Network
Vendors who operate on Torzon Market specialize in stealth packaging and discreet delivery. Standard practices include vacuum sealing, odor-proof packaging, disguised return addresses, and vacuum-formed thermal inserts to defeat scanning systems. High-trust vendors display detailed stealth descriptions and offer different stealth tiers based on package content and destination risk.
Anonymous Account System
Torzon accounts require no personally identifying information. Registration requires only a username and password. There are no email verification requirements, phone numbers, or KYC processes. Account security relies on strong passwords, optional 2FA (TOTP or PGP), and proper OPSEC from the user side. No account data is linked to real-world identities by design.
High Availability Infrastructure
Torzon Market maintains multiple onion mirrors to ensure continuous availability. Load balancing across hidden service introduction points prevents single points of failure. The platform's 99%+ uptime record is maintained through distributed infrastructure and automated failover systems. DDoS mitigation is built into the Tor hidden service architecture itself.
Vendor System & Onboarding
Becoming a vendor on Torzon Onion requires a more rigorous process than simply creating a buyer account. This friction is intentional — it creates accountability and reduces exit scam risk. The vendor onboarding process includes:
- Pay a non-refundable vendor bond (cryptocurrency deposit) — amounts vary by market tier
- Submit application details reviewed by market administrators within 24-48 hours
- Generate and publish a PGP key pair — this becomes the vendor's cryptographic identity
- Create initial product listings with detailed descriptions, photos, and stealth details
- Complete a probationary period where FE (finalize early) is not permitted
- Build reputation through verified transactions before accessing advanced vendor features
Vendor bonds are partially or fully refundable upon voluntary exit from the market in good standing. This creates a financial disincentive for exit scams — a vendor who has built substantial reputation and paid a significant bond has strong incentive to maintain that reputation rather than abscond with a single large order.
Security Architecture
Security on the Torzon darknet platform is a multi-layered system combining network-level anonymity (Tor), cryptographic authentication (PGP), financial privacy (Monero multisig), and operational security practices enforced at both the platform and user level.
