Torzon Market Statistics: Q1 2026 Report
A comprehensive look at Torzon's activity, vendor growth, and listing categories in the first quarter of 2026.
READ MOREThis portal provides independent, educational information about Torzon Onion — one of the most established darknet marketplaces operating on the Tor network. All data presented here is sourced from open research and is provided strictly for informational purposes.
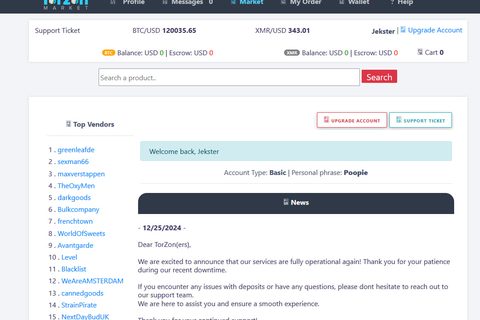
Torzon Market is a privacy-focused darknet marketplace accessible exclusively through the Tor network. Operating since 2022, it has emerged as a reliable platform within the darknet ecosystem, emphasizing vendor accountability, buyer protection, and strong operational security standards.
The Torzon darknet platform operates on a principle of strong anonymity and user protection. Unlike centralized platforms, Torzon Market distributes trust through cryptographic escrow systems, ensuring neither buyers nor vendors can defraud each other without leaving traceable evidence. Vendor accounts require substantial bond deposits and undergo review before activation.
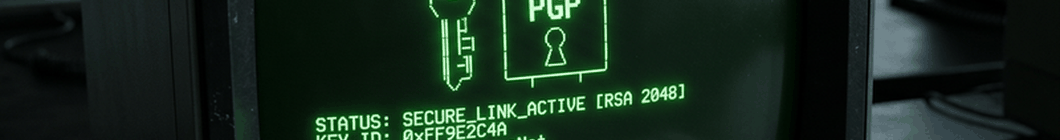
Accessing the marketplace requires the Tor Browser and a verified Torzon URL — always check links against PGP-signed announcements or our verified links page. Phishing sites are common in the darknet ecosystem, and using an unverified address can result in credential theft and fund loss.
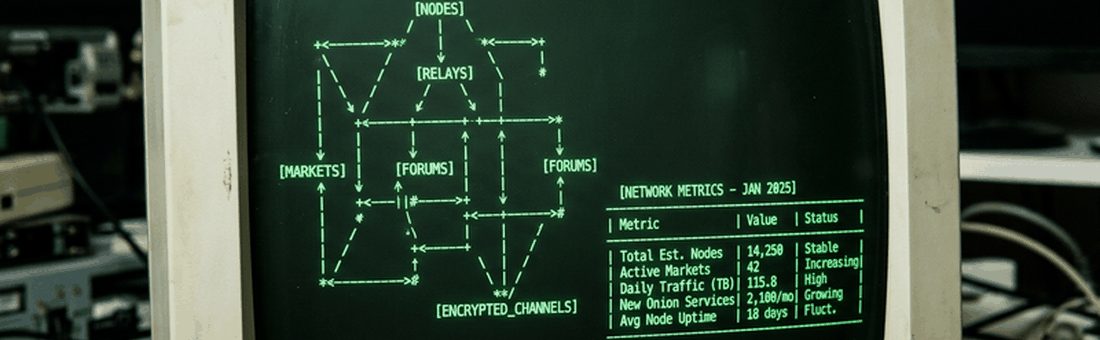
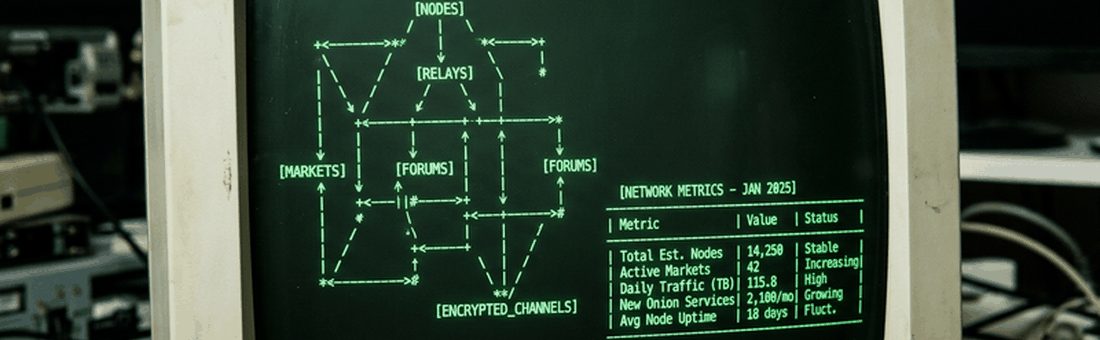
All traffic is routed through the Tor network using multi-hop onion routing, ensuring neither buyer nor vendor IP addresses are ever exposed to the other party or to the marketplace infrastructure.
Funds are held in multi-signature cryptocurrency escrow until delivery is confirmed. Neither the market nor the vendor can release funds without the buyer's cryptographic signature.

All vendor-to-buyer communications are PGP-encrypted by default. Vendors are required to publish and verify PGP keys, and the platform supports 4096-bit RSA key pairs for maximum security.
Monero (XMR) is the primary payment method, offering ring signatures, stealth addresses, and RingCT to make all transactions unlinkable and untraceable on the blockchain.

A comprehensive reputation system with verified transaction history, buyer reviews, and trust scores prevents fraudulent vendors from operating. Bonds and identity verification add additional layers of accountability.
An integrated dispute system with trained arbitrators handles conflicts between buyers and vendors. Arbitration is cryptographically logged and decisions are based on provable evidence submitted by both parties.
Understanding cryptocurrency privacy is essential for safe darknet operation. Torzon Market accepts two cryptocurrencies, each with different privacy characteristics.
Cryptocurrency became the backbone of darknet commerce as it enables pseudonymous, borderless transactions without requiring traditional financial infrastructure. Early darknet markets used Bitcoin exclusively, but its transparent blockchain quickly became a liability — law enforcement agencies developed blockchain analytics tools that could trace transactions back to real identities.
Privacy coins emerged as a response to this surveillance problem. Unlike Bitcoin, where all transactions are publicly visible on the blockchain, privacy coins use cryptographic techniques to obscure sender, receiver, and transaction amounts.
Monero is widely considered the gold standard for private cryptocurrency transactions. It uses three privacy technologies simultaneously:
Bitcoin offers pseudonymous transactions — not anonymous. All transactions are permanently visible on the public blockchain. Blockchain analytics firms can often link Bitcoin transactions to real identities without additional privacy measures.
Recent developments, security updates, and analysis from the Torzon darknet ecosystem.
A comprehensive look at Torzon's activity, vendor growth, and listing categories in the first quarter of 2026.
READ MORE
How experienced vendors package and ship physical goods to minimize detection and ensure safe delivery.
READ MORE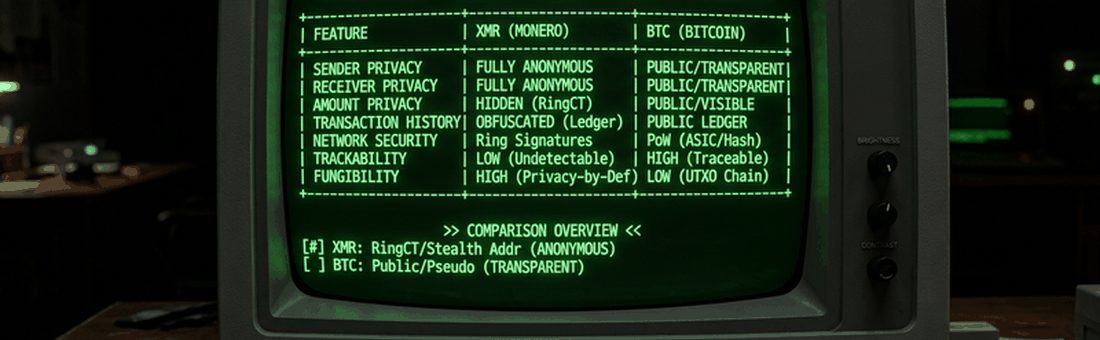
A detailed technical comparison of VPN and Tor for darknet users, explaining when each tool is appropriate and how they complement each other.
READ MORE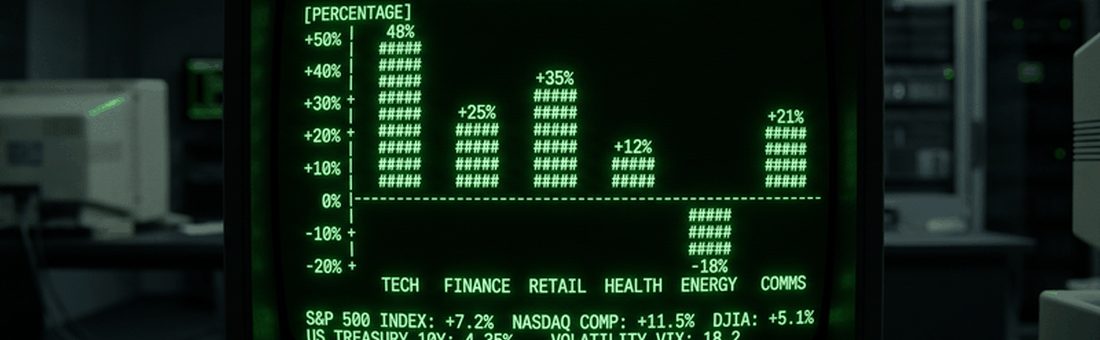
Step-by-step guide to verifying Torzon onion addresses using PGP signatures and trusted verification channels.
READ MORE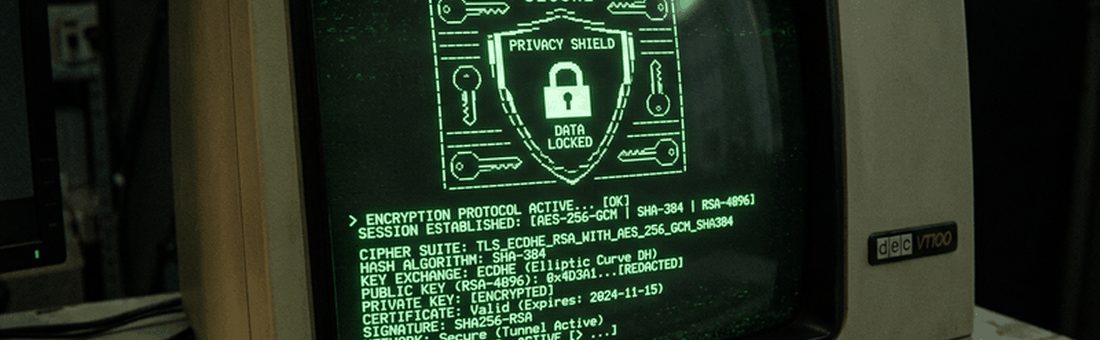
Analysis of known law enforcement techniques used to de-anonymize darknet users, and evidence-based countermeasures.
READ MORE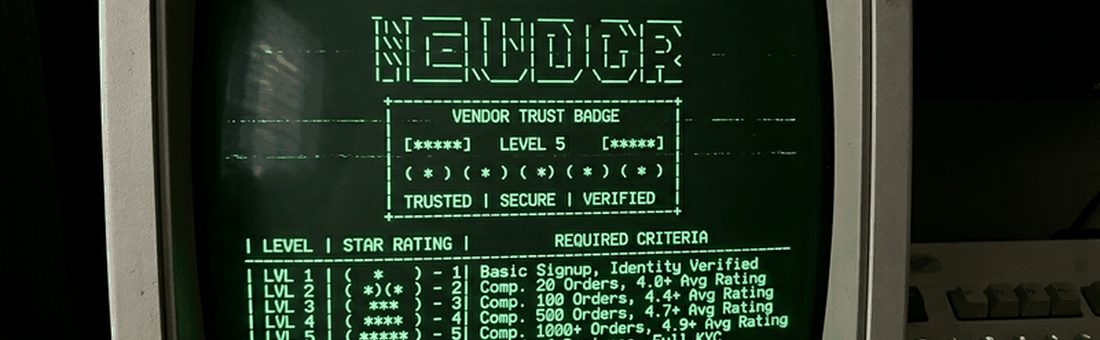
The arbitration system receives major improvements with faster resolution times and clearer evidence submission guidelines.
READ MORE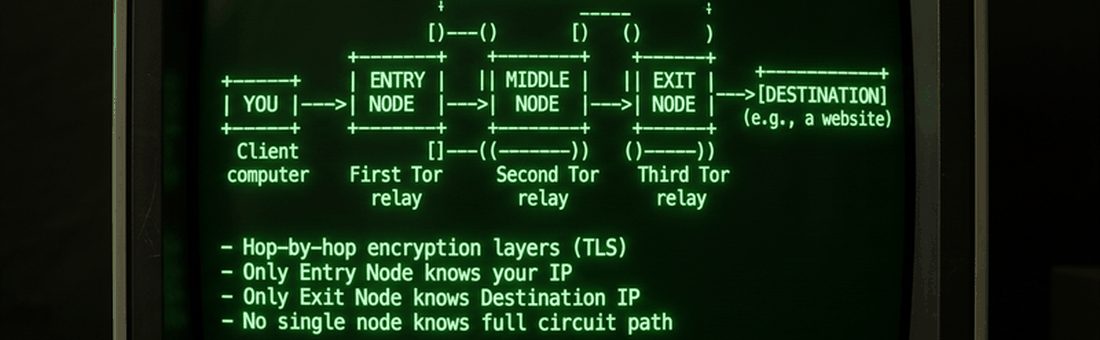
An educational look at Bitcoin CoinJoin, mixers, and privacy wallets for users who must use BTC instead of Monero.
READ MORE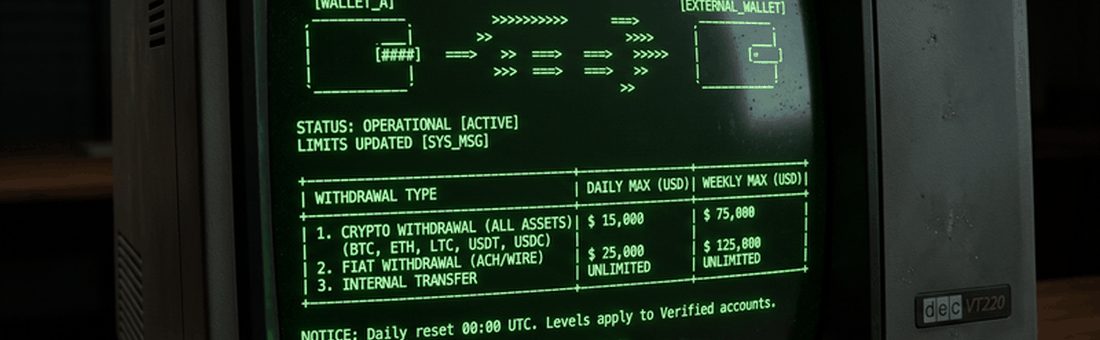
Links and descriptions of the most reliable harm reduction organizations, drug checking services, and overdose prevention resources.
READ MORE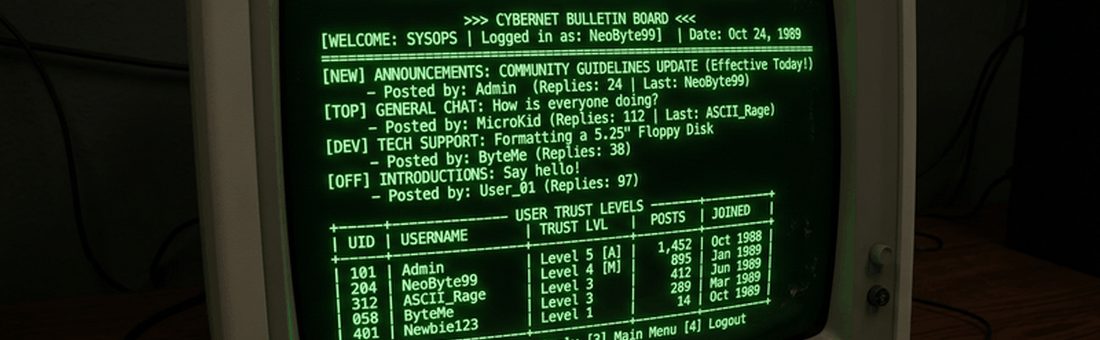
Torzon Market introduces enhanced vendor verification, exit scam detection algorithms, and improved escrow dispute timelines.
READ MOREEvidence-based harm reduction practices for individuals who choose to use substances. This information is provided without judgment and based on public health research.
Operational security (OPSEC) is the practice of protecting sensitive information and activities from adversaries. On the darknet, strong OPSEC is not optional — it is the difference between safety and exposure.
Phishing is the most common attack vector against darknet market users. Fake sites impersonating Torzon Onion steal login credentials and cryptocurrency deposits daily.
Use only verified Torzon onion addresses. Verify the URL against our PGP-signed list before entering any credentials or depositing funds.
[ PROCEED TO VERIFIED LOGIN ]